I’ve been running an OpenVPN WiFi access point on my Raspberry Pi for a while now. This AP tunnels my devices seamlessly to a VPN server in Finland – for example, ChromeCast, Android tablets etc.
The performance has been usable, but not great. I should be able to get over 30 Mbps over my current Internet connection, using the VPN server of Nebula in Helsinki, Finland. The original Pi is not that great in the CPU performance department and additionally it seemed like it was not able to handle the interrupts generated by the Ralink RT2870/RT3070 based cheapo WiFi USB dongle either.
So when the Pi2 was announced and after I figured that software-wise, it’s going to be a drop-in replacement if you’re running the most up to date version of Raspbian (a very nice job, by the way!), I ordered it to see how much things would improve.
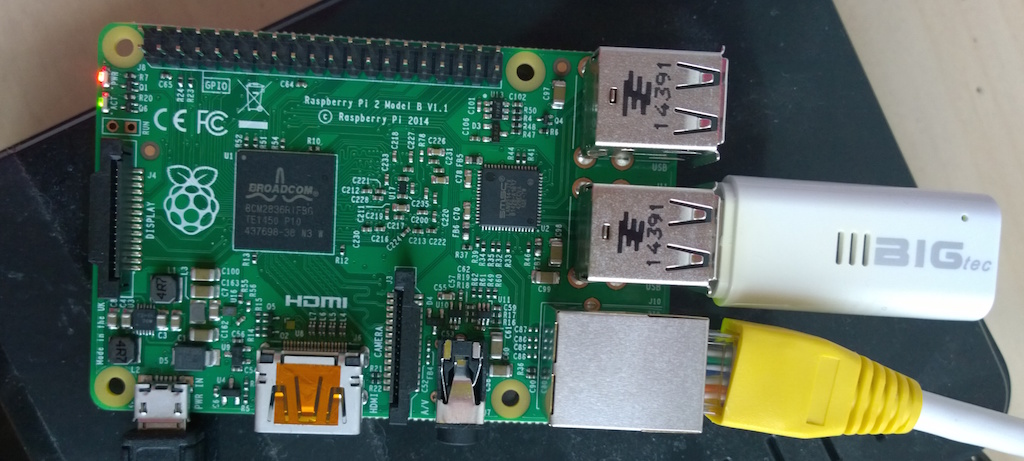
It arrived yesterday and after transferring my SD card image to an Micro-SD card, I just connected the cables and booted it up. Yep, it Just Worked(tm). After a while I figured it’s still applying the overclocking settings meant for my old Pi, and selected the new frequencies meant for the Pi2 in raspi-config. I even bothered to try to make my Prolific PL2303 USB-serial adapter to work with my Mac again (it broke sometime after I upgraded to Mavericks or Yosemite) to make analyzing the board easier. For that, I found that the following driver package worked after rebooting my machine:
http://changux.co/osx-installer-to-pl2303-serial-usb-on-osx-lio/
So everything apparently works now, and I did some non-scientific quick and dirty benchmarks using the infamous Speedtest.net application. I ran the same benchmark against the same target server three times and picked the best result out of the three. Here they are:
- Raspberry Pi 1, running at 700MHz: 5.34 Mbps
- Raspberry Pi 2, running at 1000Mhz: 17.06 Mbps
- Raspberry Pi 2, running at 1150Mhz (see below): 18.11 Mbps
- Core i7-4771 PC running at 3.5GHz: 34.99 Mbps
So, a huge improvement and as easy as it can be; however there is still room for improvement. Maybe there are ways to tune the OpenSSL setup for improved performance?
Update1 23.02.2015:
Soon after I wrote this article, I started to experience problems with clients dropping off from the WiFi AP all the time, and this showed up in the /var/log/daemon.log:
hostapd: wlan0: STA xx:xx:xx:xx:xx:xx IEEE 802.11: deauthenticated due to inactivityI workaround suggested on the Internets – to disable WMM by putting
wmm=0
into hostapd.conf, did not help. What did seem to help though was to update my board’s firmware, kernel, modules etc. with the rpi-update command. It’s been running fine for a day now.
Update2 28.2.2015
I started experimenting with overclocking. When I posted the results above my Raspi was running with the following overclocking settings:
arm_freq=1000 core_freq=500 sdram_freq=500 over_voltage=2
My VPN provider uses the 128-bit Blowfish cipher so this is the most important CPu benchmark I can use. With these settings, the command
openssl speed bf-cbc
reported the following results:
blowfish cbc 19095.24k 21153.30k 21657.60k 21785.94k 21826.22k
. After some experiments I ended up with these settings:
arm_freq=1150 core_freq=530 sdram_freq=530 over_voltage=8
With these settings the openssl benchmark reported
blowfish cbc 21917.48k 24319.51k 24907.61k 25054.21k 25100.29k
which is roughly a 15% increase. However this only translated into a Speedtest.net speed increase from 17.06 to 18.11 Mbps, which is not that much. Even so, I believe more could be gained from increasing the Blowfish processing speed further. Other things to try are to test with a “better” WiFi dongle and figuring out if OpenSSL can be tuned somehow for more performance.
Update3 18.5.2015:
The “deactived due to inactivity” problem was not really solved by updating the firmware. I finally tried putting the WiFi dongle in a powered USB 2.0 hub, and it has been working stable ever since.
My VPN provider has some problems and their server is nowadays too slow for any serious use. I tried a new one – I found another VPN provider with a Finnish server that gives you a OpenVPN config file – and now I have good performance again.
Hi
I’m facing similar issues with the Pi 2, OpenVPN throughput is around 3 Mbps, whereas running directly through Android OpenVPN client gives roughly 18 Mbps. Can you tell me which USB dongles are being used? I have two – one Edimax EW-7811Un (Realtek RTL8188CUS) for connecting to LAN and Tenda W311MI (Ralink RT5370) for the hosted AP. The Edimax dongle also shows a lot of dropped packets.
I was wondering if changing to better dongles will help improve throughput. Any thoughts?
Thanks
I am using the builtin LAN port and an Edimax dongle with the Ralink rt3070 (if I remember correctly) for Wifi.
The Wifi dongle was showing lots of dropped packets on the original Raspberry Pi 1, but on the Pi 2 it’s doing fine.
Nowadays I’m running on a Radxa Rock Lite board for the improved Blowfish decode speed, I should put up some results from that as well.
Hi Toni, would it be possible for you to share an image or an how to guide of the Radxa Rock Lite setup as an WIFI VPN gateway? many thanks!!
Hi,
I was going to do exactly that, and add some benchmark numbers as well, but I haven’t had the time…
Briefly the idea is exactly the same as with a Raspberry Pi 2 but with some complications. Most of the Linux images for the Radxa Rock Lite board were not functional when I was setting it up. The one that was was the Ubuntu Server image from July 2015. It had additional challenges in that the included hostapd did not support the builtin wifi chip. I had to rebuild that. As I remember that was the only tricky part to get right, but now it’s all working OK. I wish I had documented my steps more closely but it was one long night of hacking